Address Resolution Protocol (ARP): Resolving Network Address Conflicts
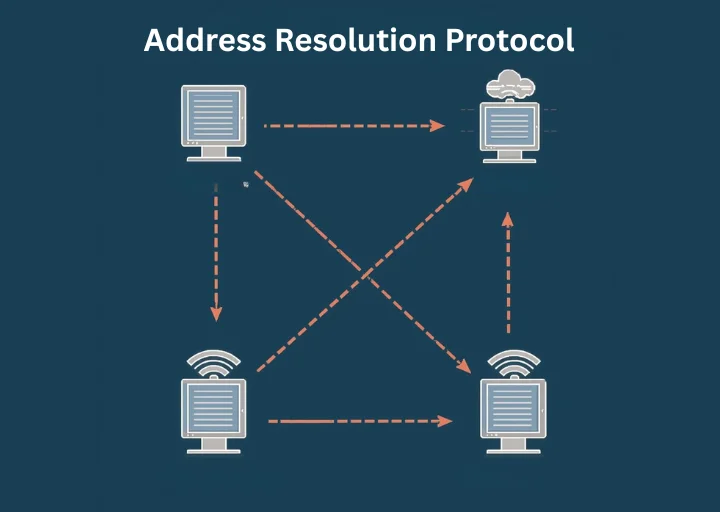
Every device on a network speaks in two identities simultaneously. One identity-the IP address-is similar to a mailing address, and it assists the data in locating its destination within the networks. The other identity-the MAC address-is attached to the hardware itself, and this guarantees accuracy in delivery after the data is sent to the local network. The means of bridging between these two identities is the Address Resolution Protocol (ARP), a core technology that silently ensures devices can talk effectively, correctly, and without any misunderstanding. The concept of ARP not only makes the operation of networks clear but also shows the equilibrium of performance, automation, and security in contemporary connectivity.
Address Resolution Protocol (ARP) Meaning
Address Resolution Protocol (ARP) is a computer protocol used in the network to identify the Internet Protocol (IP) address of a device to its physical Media Access Control (MAC) address in a local area network (LAN). An IP address is dynamically assigned and may alter with time, but the MAC address is fixed, and it is hard-coded into the network interface hardware. ARP acts as the interpreter between these two types of addresses which facilitate the devices to identify and refer to each other.
The translation of IP and MAC addresses is required due to the difference in the format of the addresses and their length. The IPv4 address has 32 bits as compared to the MAC address, which has 48 bits. Devices would not be identified to associate logical IP addresses with the actual physical hardware to send and receive data without ARP.
ARP is also adopted in the Open Systems Interconnection (OSI) model, which breaks down the networking functions into layers. The data link layer includes a MAC address that deals with the communication between the machines of the same physical network. The IP address, however, belongs to the network level, which deals with the routing of data between the networks. ARP works between the two layers and enables the possible transfer of data between logical and physical delivery.
What Does ARP Do and How Does It Work?
After a device has been connected to a LAN, it is allocated a special IP address, which identifies the device in the respective network. However, so as to pass through the information in the same locality, the MAC address of the receiving device should also be present in the device. Here, ARP is of vital concern.
When the data in a gateway is received by the gateway bound to a destination IP address, the gateway complies by looking up its ARP cache, which is a temporary storage that has stored known mappings between IP and MAC addresses. The communication is accomplished promptly in case the mapping is already in place.
In case the mapping is not located, the device sends an ARP request to the network. This query is basically the request, What device is this IP address? The device having the same IP replies with its MAC address. Upon receipt, this information is saved to the ARP cache to be used at a later point without having to incur numerous broadcasts.
ARP caches are made to be short-lived and self-contained. Entries are stored temporarily, after which they are automatically deleted to release space to facilitate security. This dynamic system is accurate, eliminates entries that are out of date, and minimizes the possibility of reusing an address without authorization.
What is ARP in Networking Useful For?
The need for ARP is linked to the fact that devices use MAC addresses during communication in the local networks, yet the users and applications utilize IP addresses. The devices could not be sure of the physical address of the data packets without ARP.
The protocol ensures that there is a maintained directory that is up-to-date with IP-to-MAC mappings. This is an automatic directory generated automatically. In the case when a machine needs to identify another machine, ARP broadcasts a request over the network. The appropriate destination replies with its MAC address, and it is stored as a point of future correspondence.
This automated technology eases the management of the network, and its connectivity is smooth. When ARP is either not available or limited, address mappings can be configured manually by the administrators, but this is inefficient and is more difficult to scale.
What Is Address Resolution Protocol’s Relationship with DHCP and DNS? How Do They Differ?
ARP is also used in conjunction with other protocols that handle device identification and communication, which include Dynamic Host Configuration Protocol (DHCP) and Domain Name System (DNS).
When devices are connected to a network, it is the duty of DHCP to give them IP addresses. Instead of using manual methods to configure every device, the DHCP will automatically assign an available IP address out of the configured range. This eliminates the occurrence of conflicts and guarantees effective address allocation.
DNS is used in a different application. It is used to convert human-understandable domain names to IP addresses. As an illustration, when a user types in the name of a website, the DNS translates this name to the IP address that is assigned in numbers, such that the device can identify the appropriate server.
ARP enhances these protocols since it ties the assigned IP address to the hardware MAC address. The combination of DHCP, DNS, and ARP forms an entire identification system enabling devices to locate, recognize, and provide each other with effective communication.
4 Key Types of ARP
ARP exists in several variations, each designed for specific networking scenarios.
Proxy ARP
Proxy ARP allows a network device to respond to ARP requests on behalf of another device located on a different network. The proxy provides its own MAC address, enabling communication without exposing the destination’s actual hardware address.
Gratuitous ARP
Gratuitous ARP is used when a device announces its own IP-to-MAC mapping to the network. This helps update other devices’ ARP caches and detect duplicate IP addresses. It is commonly used during network configuration changes.
Reverse ARP (RARP)
Reverse ARP helps devices discover their own IP addresses using their MAC addresses. This was historically useful for diskless workstations that relied on network servers for configuration.
Inverse ARP (IARP)
Inverse ARP performs the opposite of traditional ARP. Instead of resolving a MAC address from an IP address, it determines the IP address associated with a known MAC address.
Benefits and Drawbacks of Using ARP in Network Communication
Benefits of ARP in Enhancing Network Performance
Enables efficient device communication: ARP ensures devices can quickly identify each other’s hardware addresses, enabling smooth data transfer across the network.
Improves network efficiency: By storing resolved mappings in its cache, ARP reduces unnecessary broadcast requests. This lowers network traffic and improves overall performance.
Supports automated configuration: ARP automatically generates address mappings without requiring manual input, making network setup faster and more scalable.
Enhances troubleshooting capabilities: Network administrators can review ARP cache entries to diagnose connectivity issues and confirm correct address mappings.
Assists in network monitoring and security analysis: Monitoring ARP activity helps detect abnormal behaviour, such as duplicate address claims or suspicious communication attempts.
Challenges Associated with ARP Use
Susceptibility to spoofing attacks: ARP has no in-built authentication that will help in spoofing attacks, where attackers change their identities to legitimate devices.
Broadcast-related network congestion: ARP packet has to be cast on the network, and this can cause more traffic and less efficiency in a large network.
Limited security protections: Since ARP was not created to promote security, it is unable to check the authenticity of the responses.
Potential unauthorized access risks: Unscrupulous devices have the capacity to act on ARP requests and disrupt critical communication if ample safeguards have not been implemented.
The Dangers of ARP Spoofing: Attacks and Security Risks
Attackers can associate their MAC address with the legitimate IP address by spoofing ARP messages in a process referred to as ARP spoofing. It is this deception that allows attackers to intercept, monitor, or modify data.
Man-in-the-Middle (MITM)
In a man-in-the-middle attack, an attacker intercepts a communication between two devices without the knowledge of the two devices. By impersonating each endpoint, the attacker is able to gain access to financial information, login credentials, or personal information.
Denial-of-Service Attacks
DDoS attacks saturate the networks with a large amount of traffic and prevent legitimate users from accessing services. ARP spoofing has the ability to redirect or block data, which is a contributor to service failures.
Session Hijacking
By stealing session identifiers, attackers can gain unauthorized access to systems, accounts, or services, impersonating users.
Best Practices for ARP Attack Prevention
Organizations can reduce ARP-related risks by implementing proactive security measures.
Use static ARP entries in critical systems: Manually defining address mappings prevents unauthorized devices from altering key network relationships.
Enable dynamic ARP inspection (DAI): DAI verifies ARP messages against trusted address information and blocks suspicious or invalid responses.
Implement port security controls: Restricting MAC addresses per switch port limits unauthorized device connections.
Control physical and wireless access: Restricting network access ensures only authorized devices can connect and participate in ARP communication.
Use encryption and VPN protection: Encrypting data ensures that even if traffic is intercepted, it cannot be easily read or exploited.
Secure Your Network Infrastructure with Effective ARP Management
ARP is at the core of facilitating local networking by converting logical IP addresses, after which they are translated to physical MAC addresses. The process will guarantee that data is presented effectively and reliably to the relevant hardware destination.
Although ARP enhances performance and automation, authentication presents security threats, including spoofing and interception, as it does not contain authentication. To protect network integrity, organizations should have protective mechanisms in place, such as surveillance, access control, and encryption.
When ARP is handled properly, the reliability of a network is improved, it is easier to troubleshoot, and the overall security posture is also improved. With the continued growth and development of networks, it is still necessary to comprehend ARP so that it remains effective and safe to communicate.
FAQs
How is ARP used?
ARP maps the IP addresses to the MAC addresses so that local network devices can be able to interact directly.
How did ARP evolve with IPv6?
In IPv6, the ARP has been superseded by the Neighbour Discovery Protocol (NDP), which is more efficient and secure.
What is the ARP cache?
ARP cache is a table containing the address mappings that have been resolved recently, so that communication is faster and repeated requests might be avoided.
What happens when ARP fails?
There might be a failure occurring in communication, resulting in connectivity problems, delays, or network failures.
What are the key product features of ARP?
ARP contains sender and target IP and MAC addresses, operation codes, and protocol headers, which allow the proper address resolution.
ARP translates logical addresses into physical ones, which allows devices to find one another within a short time and to interact within a short time without interruption. The contribution of this one might not be visible to the users yet, but without it, modern networking would be less efficient and reliable than it is now.

Principal Consultant